41 | Add to Reading ListSource URL: www.forvaltningsrattenistockholm.domstol.seLanguage: English - Date: 2014-02-25 08:16:28
|
|---|
42 | Add to Reading ListSource URL: mttgroup.chLanguage: English - Date: 2014-11-18 04:09:23
|
|---|
43 | Add to Reading ListSource URL: www.l-3ar.comLanguage: English - Date: 2014-08-21 11:16:05
|
|---|
44 | Add to Reading ListSource URL: www.blackhat.comLanguage: English - Date: 2014-12-16 19:06:37
|
|---|
45 | Add to Reading ListSource URL: www.litescape.comLanguage: English - Date: 2010-06-29 20:11:55
|
|---|
46 | Add to Reading ListSource URL: www.ctcomp.comLanguage: English - Date: 2015-04-06 15:05:00
|
|---|
47 | Add to Reading ListSource URL: www.datatel.co.thLanguage: English - Date: 2010-07-24 13:42:22
|
|---|
48 | Add to Reading ListSource URL: www.mttgroup.chLanguage: English - Date: 2014-11-18 04:09:23
|
|---|
49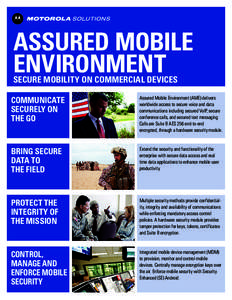 | Add to Reading ListSource URL: www.motorolasolutions.comLanguage: English - Date: 2015-03-19 15:35:12
|
|---|
50 | Add to Reading ListSource URL: cups.cs.cmu.eduLanguage: English - Date: 2013-05-31 08:50:04
|
|---|